Introducing two new governance capabilities to Vendia MCP Gateway: Security Guardrails for automated PII/PHI detection and Rate Limiting for fine-grained traffic control. Together, these features give workspace administrators comprehensive tools to enforce data privacy policies and manage resource usage across users and API credentials.
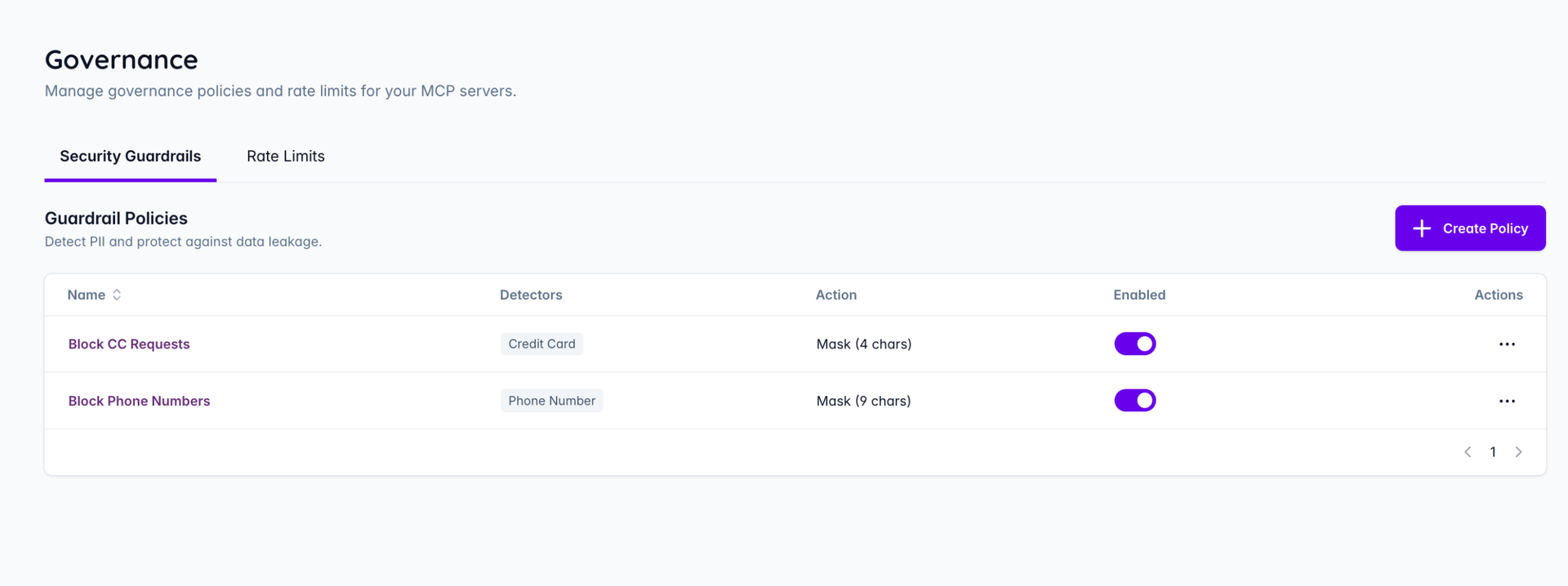
Security Guardrails for PII/PHI Detection
AI agents can retrieve sensitive data from backend systems via MCP tool calls and pass it directly to LLMs or external services — often without any inspection in between.
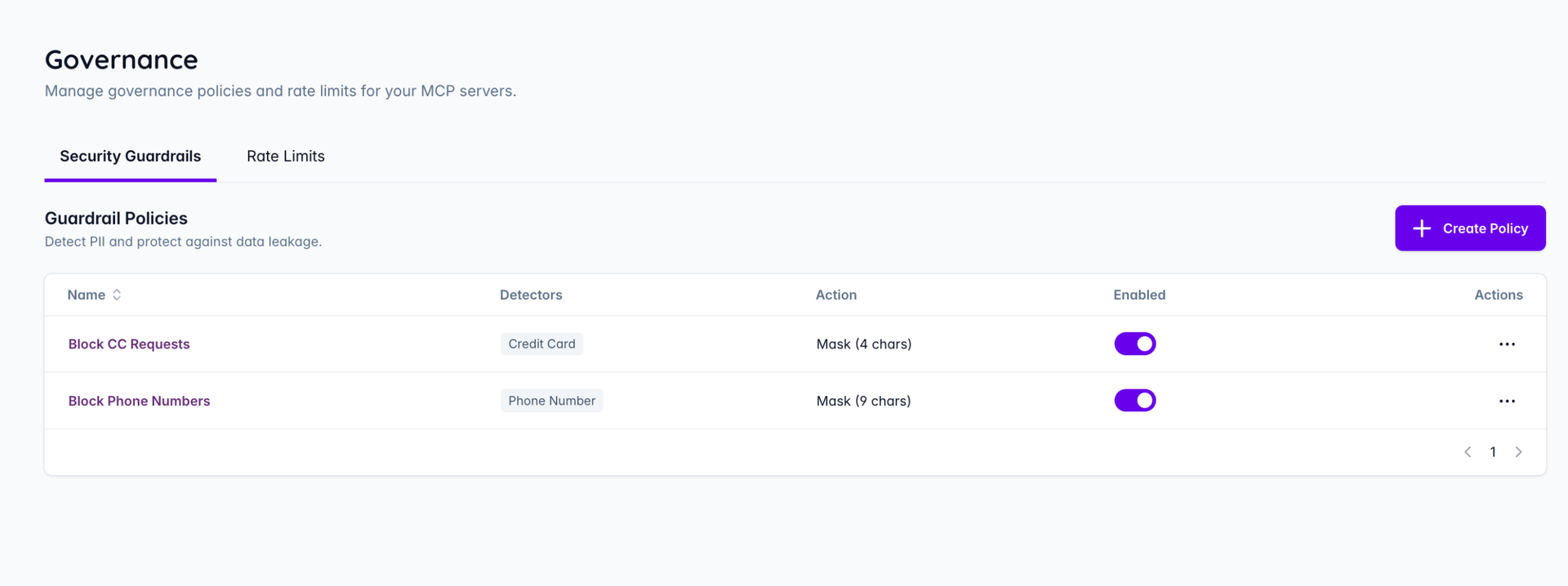
Guardrail Policies let administrators intercept that traffic, detect sensitive data, and act on it before it leaves the gateway.
How it works:
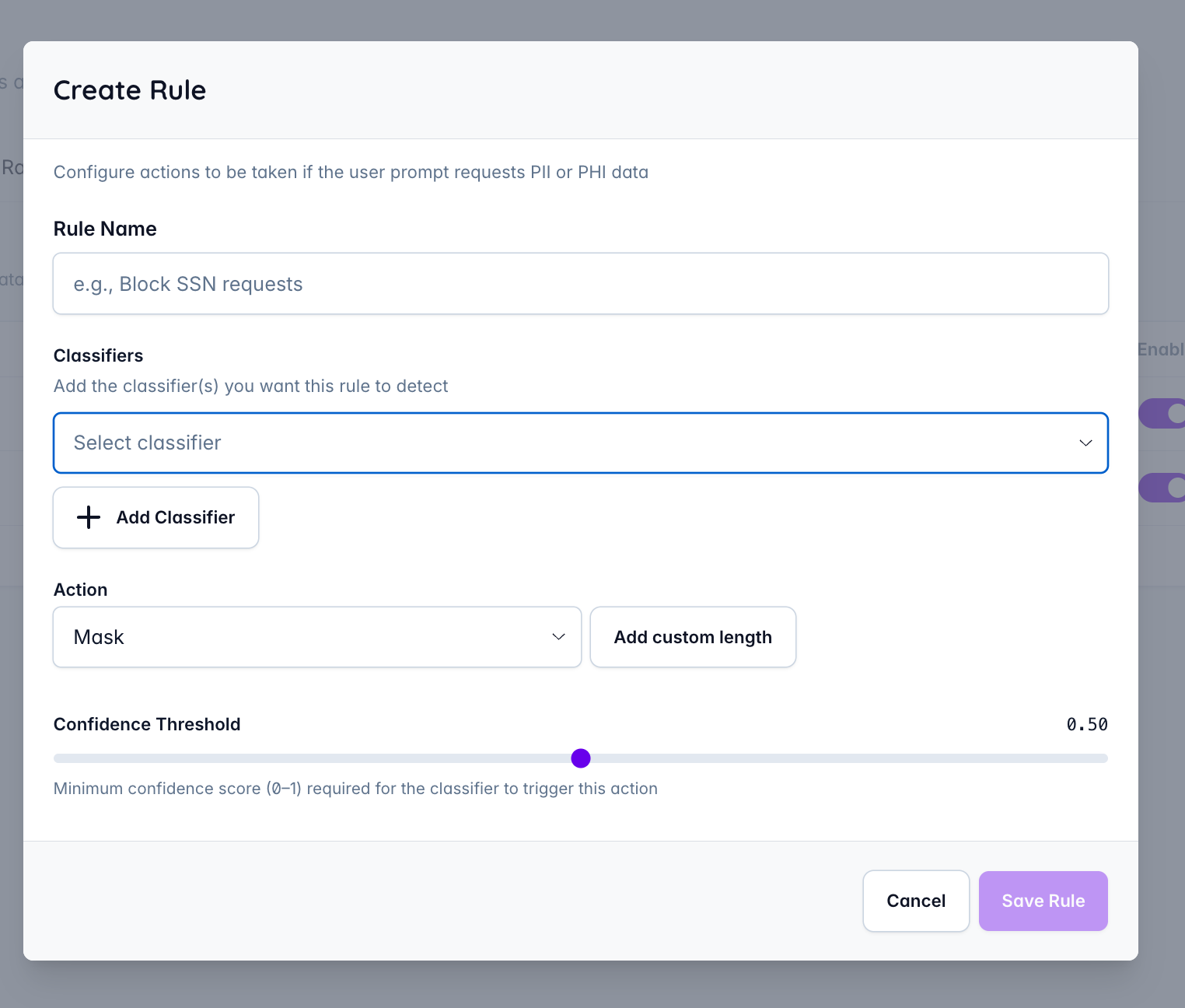
Each policy pairs one or more classifiers (data types to detect) with an action and a confidence threshold.
Policies can be enabled or disabled individually without deletion.
Supported Classifiers: Credit Card, Crypto Wallet, Date/Time, Email Address, IBAN Code, IP Address, Location, Medical License, NRP (Nationality/Religion/Political group), Person, Phone Number, URL, US Bank Number, US Driver License, US ITIN, US Passport, US SSN, Person, Phone Number, URL, US Bank Number, US Driver License, US ITIN, US Passport, and US SSN.
Audit Trail Integration
Every guardrail trigger is automatically recorded in the Vendia Audit Trail. Each entry captures:
This gives administrators a tamper-evident log across all MCP traffic — useful for SOC 2 and GDPR compliance reporting, incident investigation, and policy tuning.
Responding to PII Detection Events
Every PII detection event emits a Vendia Change Data Event in real-time, enabling automated response workflows downstream. Teams can use these events to trigger actions such as:
Rate Limiting
Plan capacity, understand adoption, and identify power users. User-level call attribution surfaces which users are driving the most activity across the gateway.
Security Guardrails are available in the Free, Pro and Enterprise tiers. For more information visit docs.vendia.com
Security Guardrails for PII/PHI Detection
AI agents can retrieve sensitive data from backend systems via MCP tool calls and pass it directly to LLMs or external services — often without any inspection in between.
Guardrail Policies let administrators intercept that traffic, detect sensitive data, and act on it before it leaves the gateway.
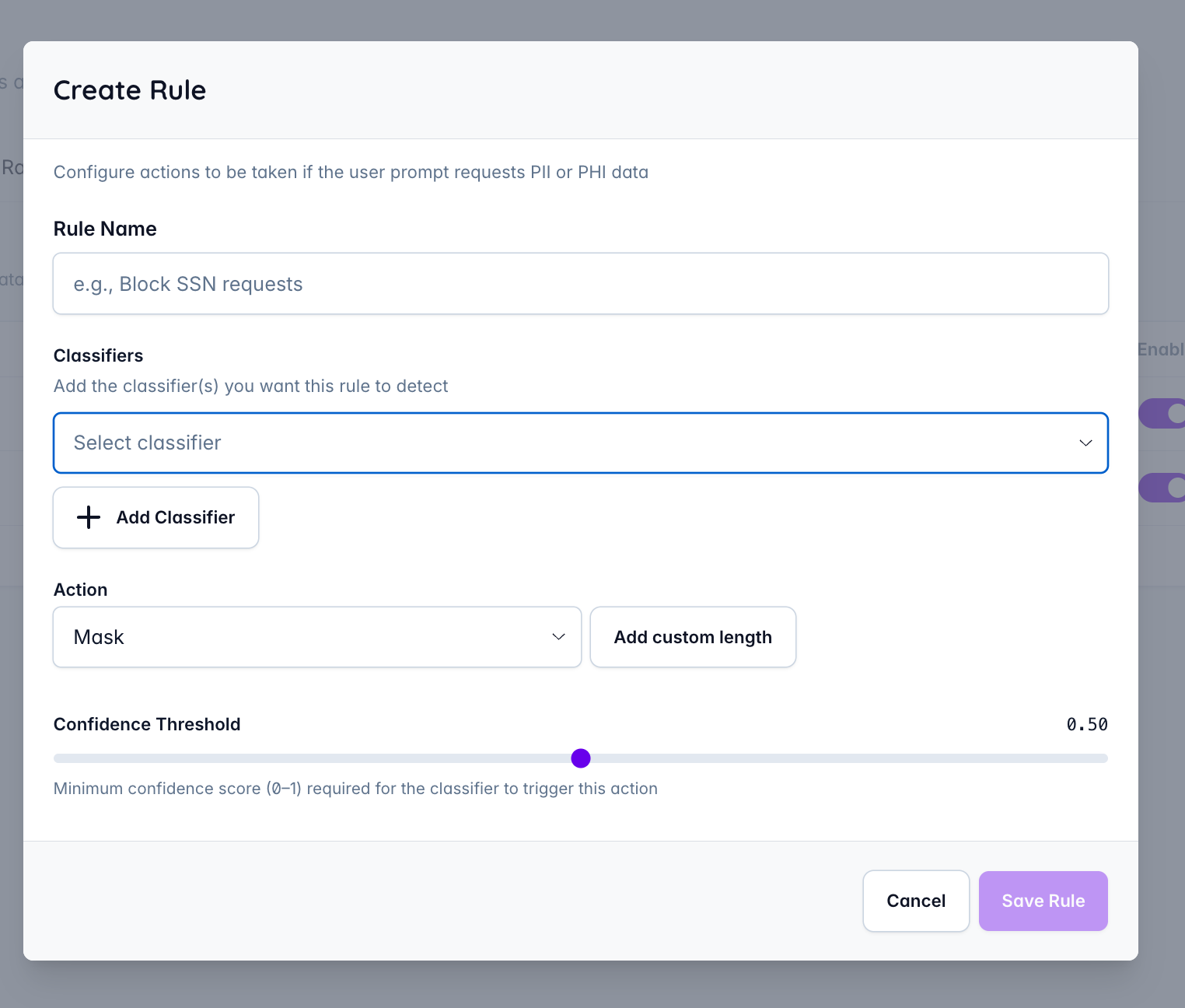
How it works:
Each policy pairs one or more classifiers (data types to detect) with an action and a confidence threshold.
- Mask — obscures the detected value before forwarding to the LLM; supports a configurable character length
- Deny — blocks the request entirely
- Notify — flags the event without altering the data
Policies can be enabled or disabled individually without deletion.
Supported Classifiers: Credit Card, Crypto Wallet, Date/Time, Email Address, IBAN Code, IP Address, Location, Medical License, NRP (Nationality/Religion/Political group), Person, Phone Number, URL, US Bank Number, US Driver License, US ITIN, US Passport, US SSN, Person, Phone Number, URL, US Bank Number, US Driver License, US ITIN, US Passport, and US SSN.
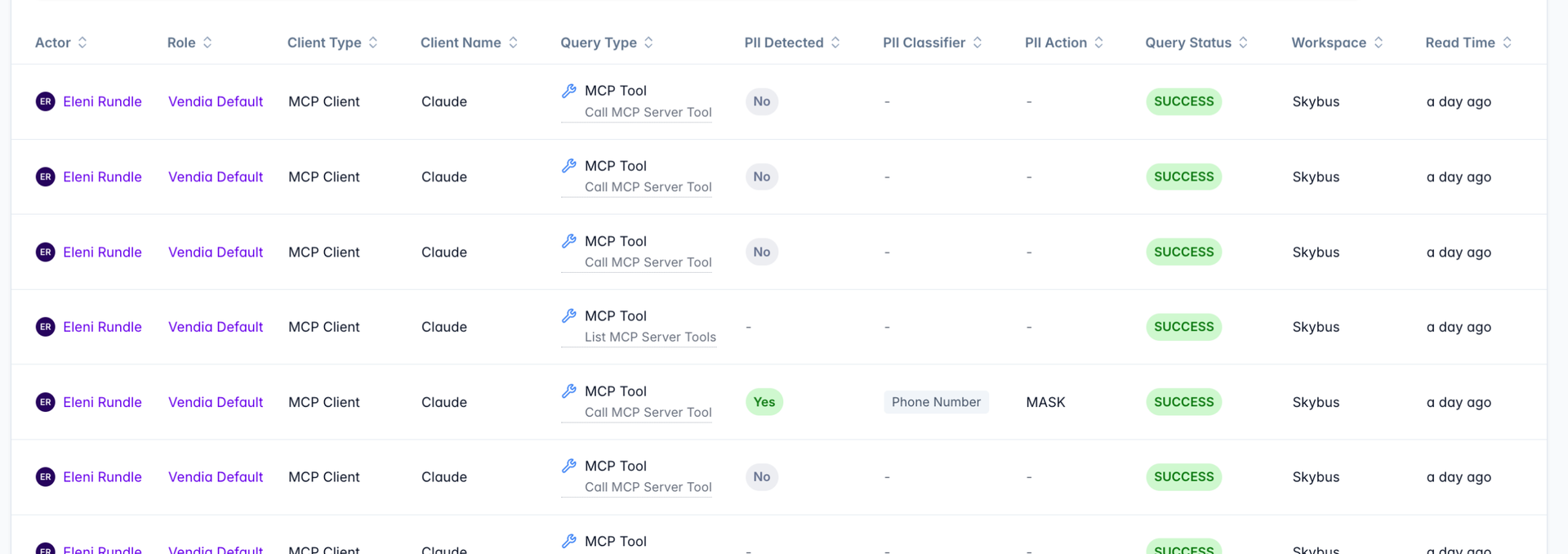
Audit Trail Integration
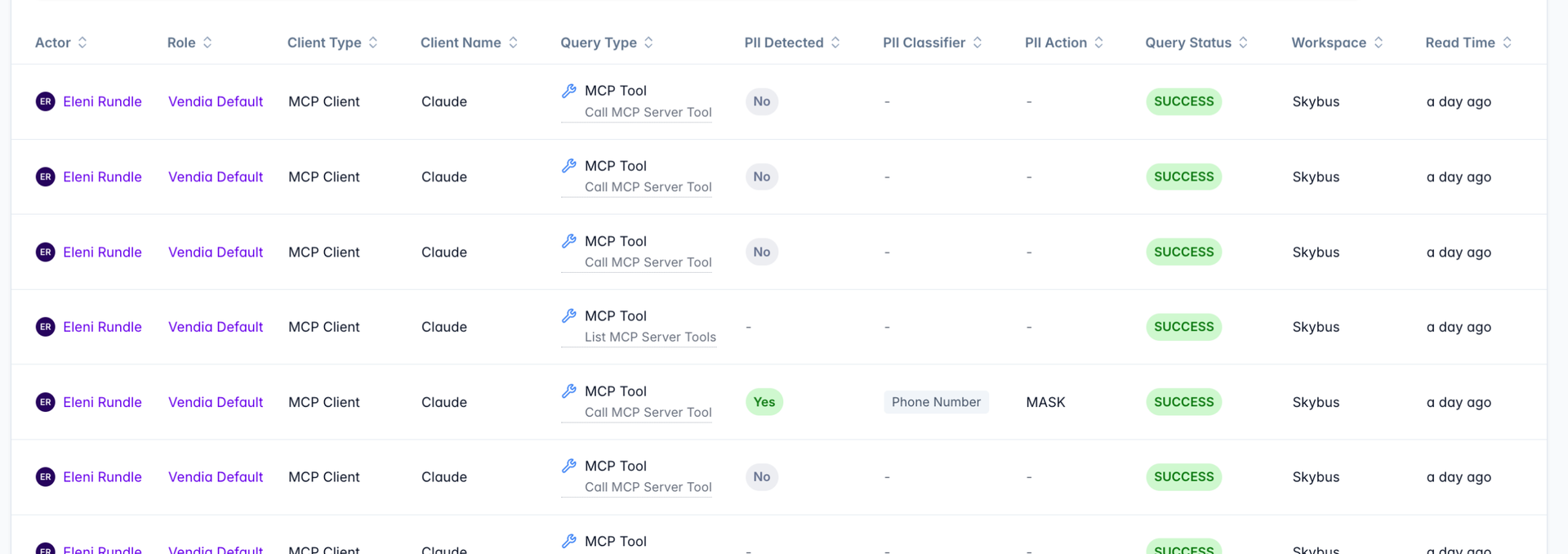
Every guardrail trigger is automatically recorded in the Vendia Audit Trail. Each entry captures:
- Actor, client type, and client name (e.g., Claude via MCP Client)
- Query type and status
- Whether PII was detected, and which classifier matched (e.g., Phone Number)
- Action taken (e.g., Mask)
- Originating workspace
This gives administrators a tamper-evident log across all MCP traffic — useful for SOC 2 and GDPR compliance reporting, incident investigation, and policy tuning.
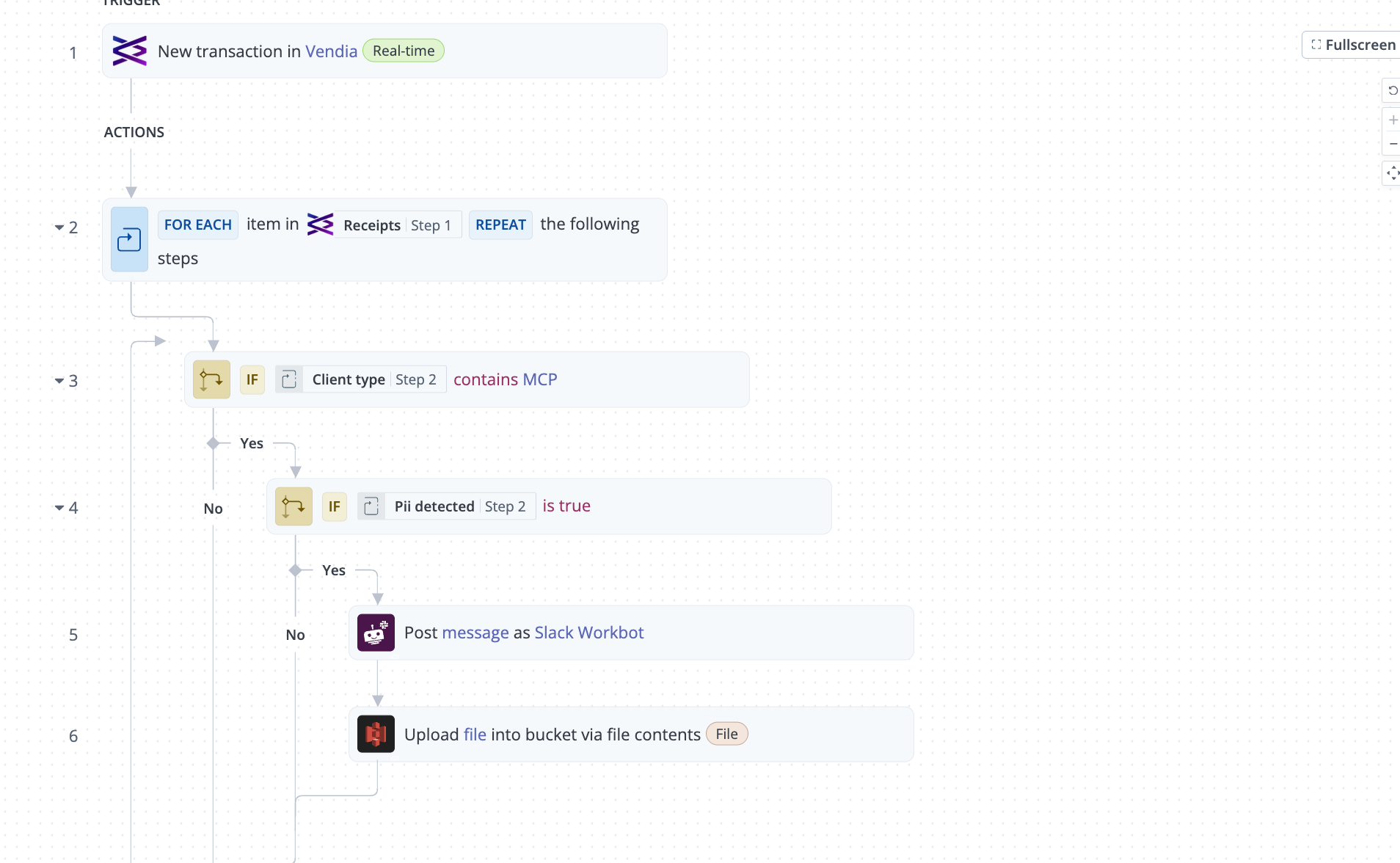
Responding to PII Detection Events
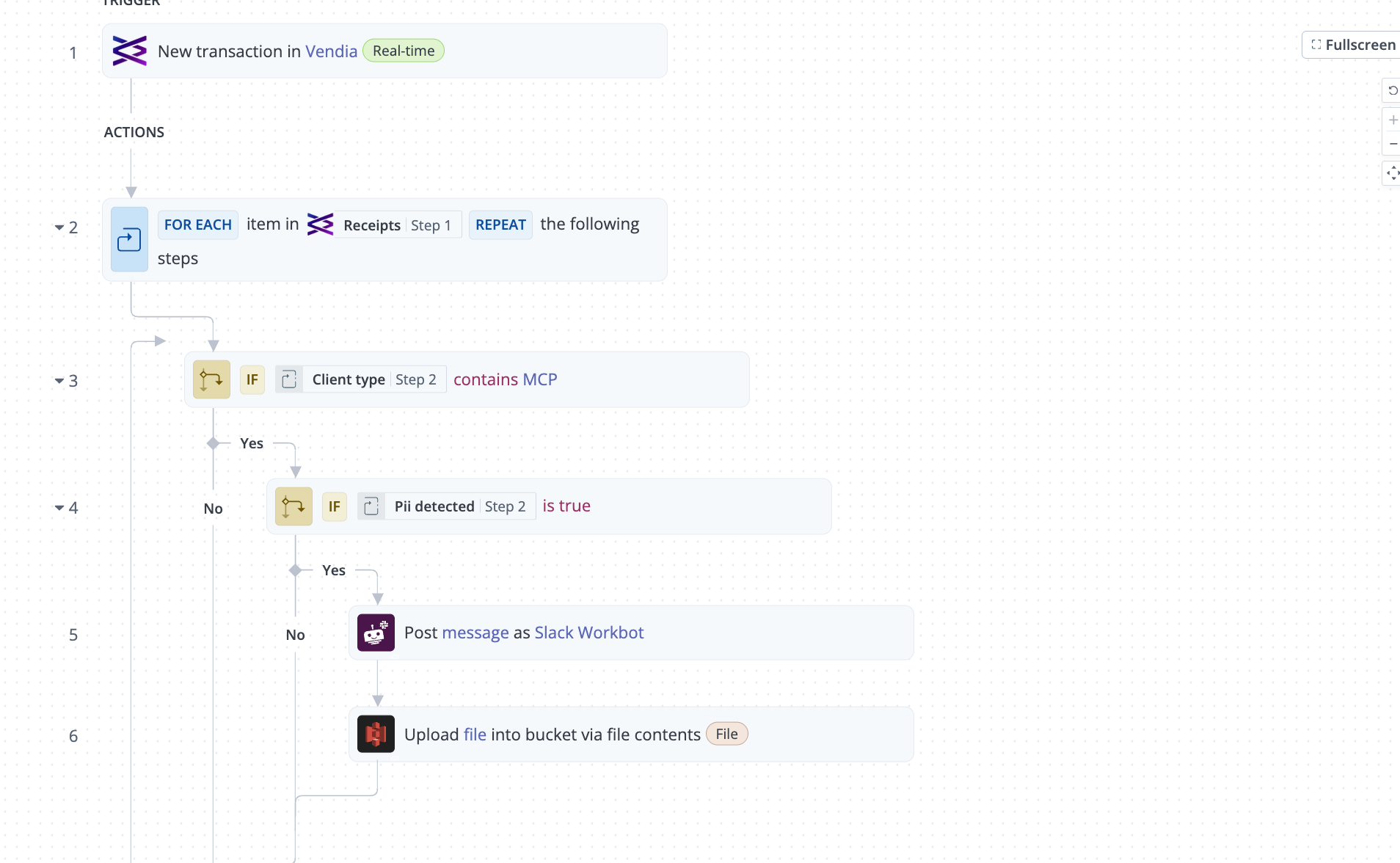
Every PII detection event emits a Vendia Change Data Event in real-time, enabling automated response workflows downstream. Teams can use these events to trigger actions such as:
- Post Slack notifications when PII is detected in an MCP request
- Upload detection records to an external storage system or data lake
- Make API calls to dynamically create or tighten a guardrail policy
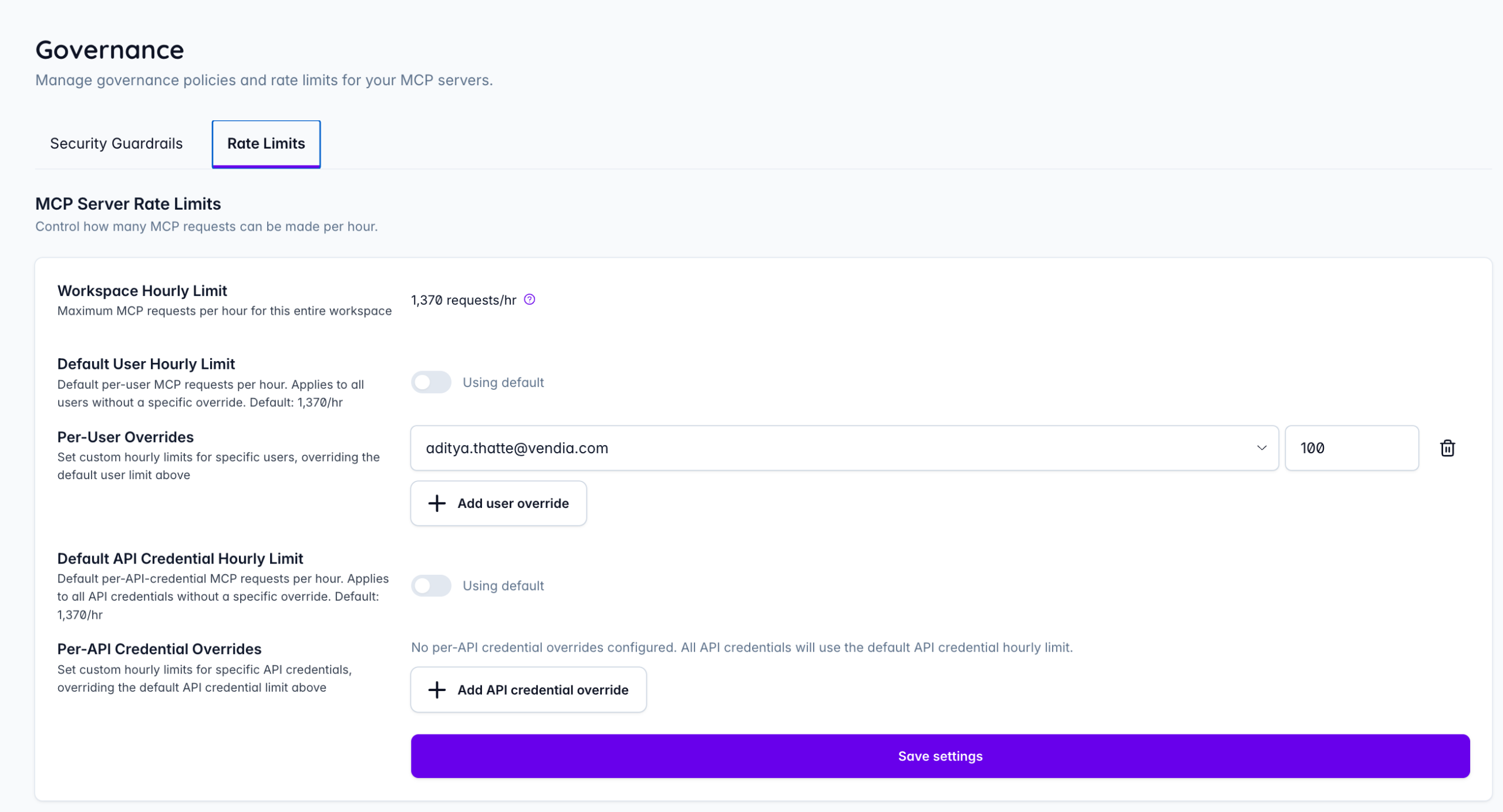
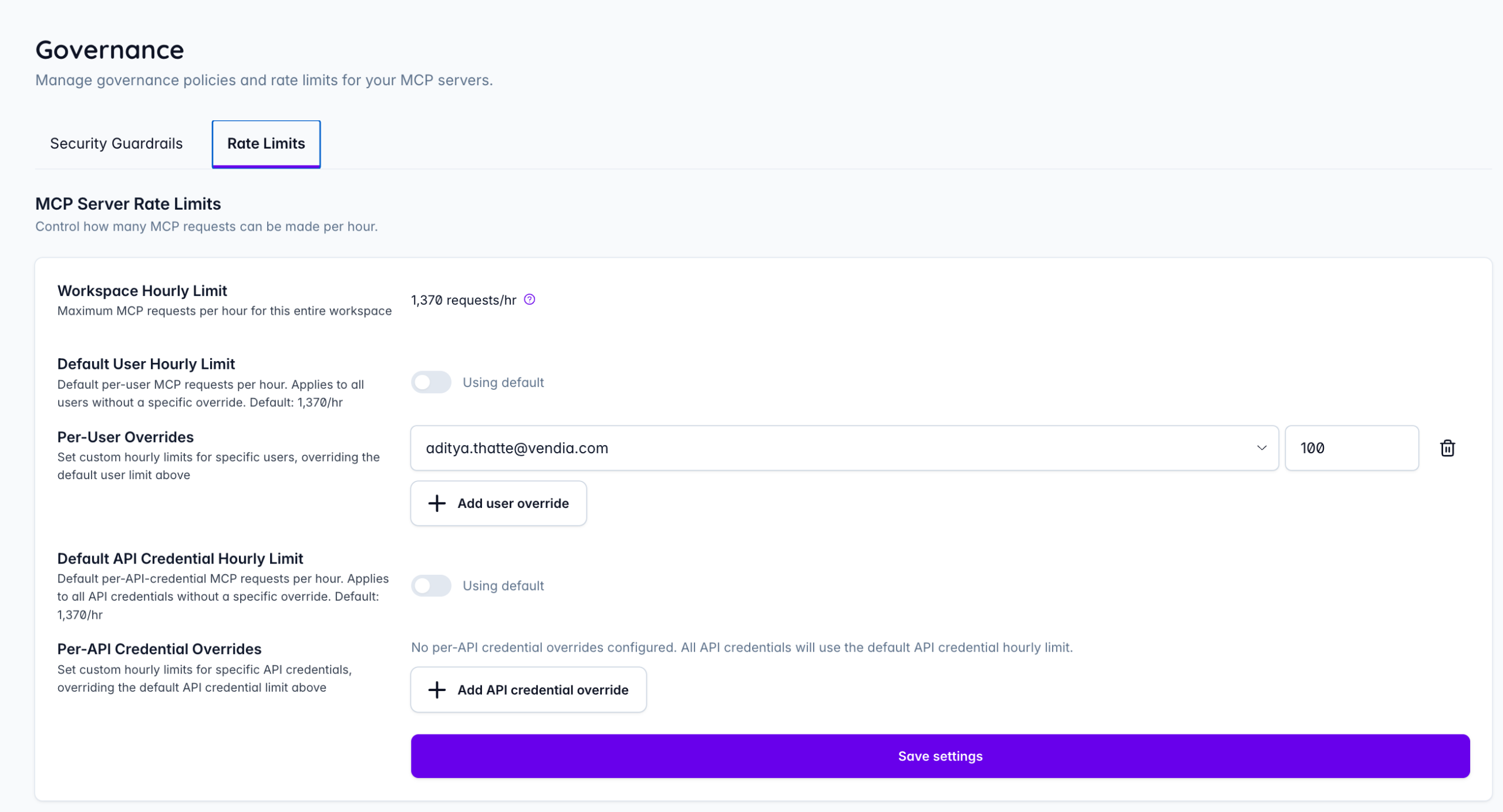
Rate Limiting
Plan capacity, understand adoption, and identify power users. User-level call attribution surfaces which users are driving the most activity across the gateway.
- Workspace hourly limit — hard ceiling on total MCP requests per hour for the entire workspace
- Per-user overrides — custom hourly limits for specific users (e.g., capped at 100 req/hr);
- Per-API credential overrides — custom limits for individual API credentials to limit agent access
Security Guardrails are available in the Free, Pro and Enterprise tiers. For more information visit docs.vendia.com